- Cookie 3 0 30 – Protect Your Online Privacy System
- Cookie 3 0 30 – Protect Your Online Privacy Slats
- Cookie 3 0 30 – Protect Your Online Privacy Act
- Cookie 3 0 30 – Protect Your Online Privacy Fence
Contact the privacy team. If you're not able to find what you're looking for, or you have a privacy question or concern—contact our privacy team. Enterprise and business customers. Check out the Microsoft Trust Center to find out how we protect your data in the Microsoft Cloud. This means websites could possibly set cookies in your browser just as if you had actually clicked the link to their website. This is a privacy drawback, and it's not needed in today's world of fast internet connections. Help Protect Me From Malicious Sites and Downloads with Windows Defender SmartScreen. Since a Safari update in 2017, third-party cookies are blocked by default. To manage your cookie settings, open Safari and click the Safari menu at the top-left (next to the Apple menu) and select Preferences. In the following window, select Privacy. Prevent cross-site tracking should be enabled by default.
-->By Rick Anderson
ASP.NET Core Identity is a complete, full-featured authentication provider for creating and maintaining logins. However, a cookie-based authentication provider without ASP.NET Core Identity can be used. For more information, see Introduction to Identity on ASP.NET Core.
View or download sample code (how to download)
For demonstration purposes in the sample app, the user account for the hypothetical user, Maria Rodriguez, is hardcoded into the app. Use the Email address maria.rodriguez@contoso.com and any password to sign in the user. The user is authenticated in the AuthenticateUser method in the Pages/Account/Login.cshtml.cs file. In a real-world example, the user would be authenticated against a database.
Configuration
In the Startup.ConfigureServices method, create the Authentication Middleware services with the AddAuthentication and AddCookie methods:
AuthenticationScheme passed to AddAuthentication sets the default authentication scheme for the app. AuthenticationScheme is useful when there are multiple instances of cookie authentication and you want to authorize with a specific scheme. Setting the AuthenticationScheme to CookieAuthenticationDefaults.AuthenticationScheme provides a value of 'Cookies' for the scheme. You can supply any string value that distinguishes the scheme.
The app's authentication scheme is different from the app's cookie authentication scheme. When a cookie authentication scheme isn't provided to AddCookie, it uses CookieAuthenticationDefaults.AuthenticationScheme ('Cookies').
The authentication cookie's IsEssential property is set to true by default. Authentication cookies are allowed when a site visitor hasn't consented to data collection. For more information, see General Data Protection Regulation (GDPR) support in ASP.NET Core.
In Startup.Configure, call UseAuthentication and UseAuthorization to set the HttpContext.User property and run Authorization Middleware for requests. Call the UseAuthentication and UseAuthorization methods before calling UseEndpoints:
The CookieAuthenticationOptions class is used to configure the authentication provider options.
Set CookieAuthenticationOptions in the service configuration for authentication in the Startup.ConfigureServices method:
Cookie Policy Middleware
Cookie Policy Middleware enables cookie policy capabilities. Adding the middleware to the app processing pipeline is order sensitive—it only affects downstream components registered in the pipeline.
Use CookiePolicyOptions provided to the Cookie Policy Middleware to control global characteristics of cookie processing and hook into cookie processing handlers when cookies are appended or deleted.
The default MinimumSameSitePolicy value is SameSiteMode.Lax to permit OAuth2 authentication. To strictly enforce a same-site policy of SameSiteMode.Strict, set the MinimumSameSitePolicy. Although this setting breaks OAuth2 and other cross-origin authentication schemes, it elevates the level of cookie security for other types of apps that don't rely on cross-origin request processing.
The Cookie Policy Middleware setting for MinimumSameSitePolicy can affect the setting of Cookie.SameSite in CookieAuthenticationOptions settings according to the matrix below.
| MinimumSameSitePolicy | Cookie.SameSite | Resultant Cookie.SameSite setting |
|---|---|---|
| SameSiteMode.None | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Lax | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Lax SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Strict SameSiteMode.Strict SameSiteMode.Strict |
Create an authentication cookie
To create a cookie holding user information, construct a ClaimsPrincipal. The user information is serialized and stored in the cookie.
Create a ClaimsIdentity with any required Claims and call SignInAsync to sign in the user:
If you would like to see code comments translated to languages other than English, let us know in this GitHub discussion issue.
SignInAsync creates an encrypted cookie and adds it to the current response. If AuthenticationScheme isn't specified, the default scheme is used.
RedirectUri is only used on a few specific paths by default, for example, the login path and logout paths. For more information see the CookieAuthenticationHandler source.
ASP.NET Core's Data Protection system is used for encryption. For an app hosted on multiple machines, load balancing across apps, or using a web farm, configure data protection to use the same key ring and app identifier.
Sign out
To sign out the current user and delete their cookie, call SignOutAsync:
If CookieAuthenticationDefaults.AuthenticationScheme (or 'Cookies') isn't used as the scheme (for example, 'ContosoCookie'), supply the scheme used when configuring the authentication provider. Otherwise, the default scheme is used.
When the browser closes it automatically deletes session based cookies (non-persistent cookies), but no cookies are cleared when an individual tab is closed. The server is not notified of tab or browser close events.
React to back-end changes
Once a cookie is created, the cookie is the single source of identity. If a user account is disabled in back-end systems:
- The app's cookie authentication system continues to process requests based on the authentication cookie.
- The user remains signed into the app as long as the authentication cookie is valid.
The ValidatePrincipal event can be used to intercept and override validation of the cookie identity. Validating the cookie on every request mitigates the risk of revoked users accessing the app.
One approach to cookie validation is based on keeping track of when the user database changes. If the database hasn't been changed since the user's cookie was issued, there's no need to re-authenticate the user if their cookie is still valid. In the sample app, the database is implemented in IUserRepository and stores a LastChanged value. When a user is updated in the database, the LastChanged value is set to the current time.
In order to invalidate a cookie when the database changes based on the LastChanged value, create the cookie with a LastChanged claim containing the current LastChanged value from the database:
To implement an override for the ValidatePrincipal event, write a method with the following signature in a class that derives from CookieAuthenticationEvents:
The following is an example implementation of CookieAuthenticationEvents:
Register the events instance during cookie service registration in the Startup.ConfigureServices method. Provide a scoped service registration for your CustomCookieAuthenticationEvents class:
Consider a situation in which the user's name is updated—a decision that doesn't affect security in any way. If you want to non-destructively update the user principal, call context.ReplacePrincipal and set the context.ShouldRenew property to true.
Warning
The approach described here is triggered on every request. Validating authentication cookies for all users on every request can result in a large performance penalty for the app.
Persistent cookies
You may want the cookie to persist across browser sessions. This persistence should only be enabled with explicit user consent with a 'Remember Me' check box on sign in or a similar mechanism.
The following code snippet creates an identity and corresponding cookie that survives through browser closures. Any sliding expiration settings previously configured are honored. If the cookie expires while the browser is closed, the browser clears the cookie once it's restarted.
Set IsPersistent to true in AuthenticationProperties:
Absolute cookie expiration
An absolute expiration time can be set with ExpiresUtc. To create a persistent cookie, IsPersistent must also be set. Otherwise, the cookie is created with a session-based lifetime and could expire either before or after the authentication ticket that it holds. When ExpiresUtc is set, it overrides the value of the ExpireTimeSpan option of CookieAuthenticationOptions, if set.
The following code snippet creates an identity and corresponding cookie that lasts for 20 minutes. This ignores any sliding expiration settings previously configured.
ASP.NET Core Identity is a complete, full-featured authentication provider for creating and maintaining logins. However, a cookie-based authentication provider without ASP.NET Core Identity can be used. For more information, see Introduction to Identity on ASP.NET Core.
View or download sample code (how to download)
For demonstration purposes in the sample app, the user account for the hypothetical user, Maria Rodriguez, is hardcoded into the app. Use the Email address maria.rodriguez@contoso.com and any password to sign in the user. The user is authenticated in the AuthenticateUser method in the Pages/Account/Login.cshtml.cs file. In a real-world example, the user would be authenticated against a database.
Configuration
If the app doesn't use the Microsoft.AspNetCore.App metapackage, create a package reference in the project file for the Microsoft.AspNetCore.Authentication.Cookies package.
In the Startup.ConfigureServices method, create the Authentication Middleware service with the AddAuthentication and AddCookie methods:
AuthenticationScheme passed to AddAuthentication sets the default authentication scheme for the app. AuthenticationScheme is useful when there are multiple instances of cookie authentication and you want to authorize with a specific scheme. Setting the AuthenticationScheme to CookieAuthenticationDefaults.AuthenticationScheme provides a value of 'Cookies' for the scheme. You can supply any string value that distinguishes the scheme.
The app's authentication scheme is different from the app's cookie authentication scheme. When a cookie authentication scheme isn't provided to AddCookie, it uses CookieAuthenticationDefaults.AuthenticationScheme ('Cookies').
The authentication cookie's IsEssential property is set to true by default. Authentication cookies are allowed when a site visitor hasn't consented to data collection. For more information, see General Data Protection Regulation (GDPR) support in ASP.NET Core.
In the Startup.Configure method, call the UseAuthentication method to invoke the Authentication Middleware that sets the HttpContext.User property. Call the UseAuthentication method before calling UseMvcWithDefaultRoute or UseMvc:
The CookieAuthenticationOptions class is used to configure the authentication provider options.
Set CookieAuthenticationOptions in the service configuration for authentication in the Startup.ConfigureServices method:
Cookie Policy Middleware
Cookie Policy Middleware enables cookie policy capabilities. Adding the middleware to the app processing pipeline is order sensitive—it only affects downstream components registered in the pipeline.
Use CookiePolicyOptions provided to the Cookie Policy Middleware to control global characteristics of cookie processing and hook into cookie processing handlers when cookies are appended or deleted.
The default MinimumSameSitePolicy value is SameSiteMode.Lax to permit OAuth2 authentication. To strictly enforce a same-site policy of SameSiteMode.Strict, set the MinimumSameSitePolicy. Although this setting breaks OAuth2 and other cross-origin authentication schemes, it elevates the level of cookie security for other types of apps that don't rely on cross-origin request processing.
The Cookie Policy Middleware setting for MinimumSameSitePolicy can affect the setting of Cookie.SameSite in CookieAuthenticationOptions settings according to the matrix below.
| MinimumSameSitePolicy | Cookie.SameSite | Resultant Cookie.SameSite setting |
|---|---|---|
| SameSiteMode.None | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Lax | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Lax SameSiteMode.Lax SameSiteMode.Strict |
| SameSiteMode.Strict | SameSiteMode.None SameSiteMode.Lax SameSiteMode.Strict | SameSiteMode.Strict SameSiteMode.Strict SameSiteMode.Strict |
Create an authentication cookie
To create a cookie holding user information, construct a ClaimsPrincipal. The user information is serialized and stored in the cookie.
Create a ClaimsIdentity with any required Claims and call SignInAsync to sign in the user:
SignInAsync creates an encrypted cookie and adds it to the current response. If AuthenticationScheme isn't specified, the default scheme is used.
ASP.NET Core's Data Protection system is used for encryption. For an app hosted on multiple machines, load balancing across apps, or using a web farm, configure data protection to use the same key ring and app identifier.
Sign out
To sign out the current user and delete their cookie, call SignOutAsync:
If CookieAuthenticationDefaults.AuthenticationScheme (or 'Cookies') isn't used as the scheme (for example, 'ContosoCookie'), supply the scheme used when configuring the authentication provider. Otherwise, the default scheme is used.
React to back-end changes
Once a cookie is created, the cookie is the single source of identity. If a user account is disabled in back-end systems:
- The app's cookie authentication system continues to process requests based on the authentication cookie.
- The user remains signed into the app as long as the authentication cookie is valid.
The ValidatePrincipal event can be used to intercept and override validation of the cookie identity. Validating the cookie on every request mitigates the risk of revoked users accessing the app.
One approach to cookie validation is based on keeping track of when the user database changes. If the database hasn't been changed since the user's cookie was issued, there's no need to re-authenticate the user if their cookie is still valid. In the sample app, the database is implemented in IUserRepository and stores a LastChanged value. When a user is updated in the database, the LastChanged value is set to the current time.
In order to invalidate a cookie when the database changes based on the LastChanged value, create the cookie with a LastChanged claim containing the current LastChanged value from the database:
To implement an override for the ValidatePrincipal event, write a method with the following signature in a class that derives from CookieAuthenticationEvents:
The following is an example implementation of CookieAuthenticationEvents:
Register the events instance during cookie service registration in the Startup.ConfigureServices method. Provide a scoped service registration for your CustomCookieAuthenticationEvents class:
Consider a situation in which the user's name is updated—a decision that doesn't affect security in any way. If you want to non-destructively update the user principal, call context.ReplacePrincipal and set the context.ShouldRenew property to true.
Warning
The approach described here is triggered on every request. Validating authentication cookies for all users on every request can result in a large performance penalty for the app.
Persistent cookies
You may want the cookie to persist across browser sessions. This persistence should only be enabled with explicit user consent with a 'Remember Me' check box on sign in or a similar mechanism.
The following code snippet creates an identity and corresponding cookie that survives through browser closures. Any sliding expiration settings previously configured are honored. If the cookie expires while the browser is closed, the browser clears the cookie once it's restarted.
Set IsPersistent to true in AuthenticationProperties:
Absolute cookie expiration
An absolute expiration time can be set with ExpiresUtc. To create a persistent cookie, IsPersistent must also be set. Otherwise, the cookie is created with a session-based lifetime and could expire either before or after the authentication ticket that it holds. When ExpiresUtc is set, it overrides the value of the ExpireTimeSpan option of CookieAuthenticationOptions, if set.
The following code snippet creates an identity and corresponding cookie that lasts for 20 minutes. This ignores any sliding expiration settings previously configured.
Additional resources
One of the best ways to protect your privacy online is to use a virtual private network (VPN). See our VPN reviews to find the best one for you.
Cookie 3 0 30 – Protect Your Online Privacy System
What's a cookie?
If you've been anywhere on the internet, you've probably heard of cookies (also known as computer cookies or HTTP cookies). These are small files that websites want to put on your computer and store in your web browser.
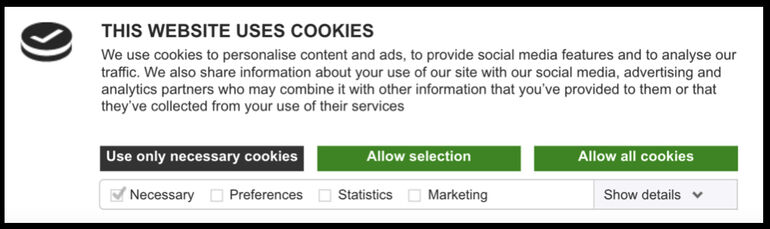
But should you accept or block cookies?
Cookies don't infect your computer with malicious software or viruses. They're basically just text files to be read by whatever website or third party put them there. They have a range of uses, some you may like more than others.
The good news is it's not an all-or-nothing affair. Most browsers let you control which kinds of cookies are allowed. Here's how to manage them in Google Chrome, Apple's Safari, and Microsoft Edge – the Windows 10 default browser that replaced Internet Explorer.
But before you decide, you need to understand what each type of cookie does.
First-party cookies
First-party cookies belong to the website you're currently on and don't track what you do on other websites.
There are two kinds of first-party cookies:
Session cookies
These are short-lived and are usually deleted when your browser closes.
Without these cookies, every time you clicked a link – even to load a new page on the same website – it would forget you'd ever been there. For example, say you're shopping online and you add an item to your cart. If you then view another item on a different page, once the new page loads your cart would be empty because there'd be no way to track what you did previously.
Or perhaps a website asked you what language you'd prefer. Without session cookies, you'd have to re-select it with each new page.
Persistent cookies
These live on in your browser after it closes, but self-destruct after a predetermined time – usually within six months. If you ever asked a website to remember your login details, it did so with a first-party persistent cookie.
Persistent cookies may also be used to remember what you read or did while you were on the site, to avoid showing you the same content if you log back on later. While some persistent cookies are first-party, not all are.
Third-party cookies
These are also persistent. They're often used for tracking your movements to gain marketing or demographic data.
If you disable third-party cookies it'll make it harder for advertisers to get information about your online activity. You'll still see ads; they just probably won't be tailored to your interests.
Third-party cookies have also been blamed for slowing down web page loading times. Some browsers, such as Safari and Firefox, block them by default. Others let you opt-out in their settings menu.
How to manage cookies in Google Chrome
Hider 2 4 9 download free. At the top-right of a browser window, click the menu button (three vertical dots), then Settings. Scroll down and click Advanced.
In the Privacy and Security section, click Content Settings then Cookies. Turning cookies off completely would disable all the features we've talked about so far, not just the tracking ones. So it's advisable to not block them entirely.
If you enable Keep local data online until you quit your browser, you'll still be able to add items to a shopping cart, but every time you close your browser you'll lose things like automatic sign-ins on your favourite websites.
Block third-party cookies stops the marketing-led cookies that track your internet usage and patterns, while leaving the more-useful cookies running.
If you'd like a fresh start with your new cookie settings, you can delete all your current ones. Click See all cookies and site data, then Remove All.
How to manage cookies in Safari (on macOS)
Since a Safari update in 2017, third-party cookies are blocked by default.
To manage your cookie settings, open Safari and click the Safari menu at the top-left (next to the Apple menu) and select Preferences. In the following window, select Privacy.
Prevent cross-site tracking should be enabled by default. This stops third-party cookies that track you across websites for advertisers.
Ask websites not to track me requests websites to not use both third-party and first-party persistent cookies. It's up to the website to respect your request.
Block all cookies will stop third-party cookies, but also the first-party cookie features mentioned earlier.
To delete the cookies you already have, click Manage Website Data and select cookies from individual websites on the list and click Remove, or select Remove all to delete the lot.
Cookie 3 0 30 – Protect Your Online Privacy Slats
How to manage cookies in Microsoft Edge
Cookie 3 0 30 – Protect Your Online Privacy Act
Click the ellipsis (…) icon at the top right and select Settings. Scroll down and under Advanced settings, select View advanced settings. Scroll down again and under Cookies there are three options: Block all cookies, Block only third party cookies and Don't block cookies.
If you want to stop other parties tracking your online activity, select Block only third party cookies. This should make it harder for targeted advertisers and data analytics firms to get information about you.
If you Block all cookies then none of the functions we mentioned earlier will work (auto login, adding items to a shopping cart, etc.) and some websites may become unusable.
Cookie 3 0 30 – Protect Your Online Privacy Fence
To delete the cookies you already have, go to Settings then under Clear browsing data, click Choose what to clear. Make sure Cookies and saved website data is ticked, then hit Clear.

